It seems people really got interested in the security of phpLiteAdmin. That’s cool, lots of people searching for security issues will give us the opportunity to fix a lot of things in a short period of time. Go on searching. We’ll go on fixing.
But some of these exploiters only publish an “exploit” that contains no real issue at all. Probably only to get some publicity, or maybe because they don’t even realize that what they “found” is not an issue at all. Or meant as a joke?
I recently found a new “security exploit” listing several “vulnerabilities”, which in fact are no bugs of phpLiteAdmin at all but misconfiguration or even features. So here I want to have a look at an “exploit” released by “KedAns-Dz”:
1-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=0
0 _ __ __ __ 1
1 /' \ __ /'__`\ /\ \__ /'__`\ 0
0 /\_, \ ___ /\_\/\_\ \ \ ___\ \ ,_\/\ \/\ \ _ ___ 1
1 \/_/\ \ /' _ `\ \/\ \/_/_\_<_ /'___\ \ \/\ \ \ \ \/\`'__\ 0
0 \ \ \/\ \/\ \ \ \ \/\ \ \ \/\ \__/\ \ \_\ \ \_\ \ \ \/ 1
1 \ \_\ \_\ \_\_\ \ \ \____/\ \____\\ \__\\ \____/\ \_\ 0
0 \/_/\/_/\/_/\ \_\ \/___/ \/____/ \/__/ \/___/ \/_/ 1
1 \ \____/ >> Exploit database separated by exploit 0
0 \/___/ type (local, remote, DoS, etc.) 1
1 1
0 [+] Site : 1337day.com 0
1 [+] Support e-mail : submit[at]1337day.com 1
0 0
1 ######################################### 1
0 I'm KedAns-Dz member from Inj3ct0r Team 1
1 ######################################### 0
0-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-==-=-=-1
Okay yeah. We know exploiters love ASCII art. Kind of cool, agreed.
###
# Title : phpLiteAdmin v1.8.x->1.9.x (SQLi/FD) <= Multiple Vulnerabilities
# Author : KedAns-Dz
# E-mail : ked-h (@hotmail.com / @1337day.com)
# Home : Hassi.Messaoud (30500) - Algeria -(00213555248701)
# Web Site : www.1337day.com .net .org
# FaCeb0ok : http://fb.me/Inj3ct0rK3d
# TwiTter : @kedans
# Friendly Sites : www.r00tw0rm.com * www.exploit-id.com
# Type : proof of concept - webapp 0day - remote - php
# Tested on : Windows7
###
# <3 <3 Greetings t0 Palestine <3 <3
# F-ck HaCking, Lov3 Explo8ting !
As I said. I like exploits as well. Even if they just make me laugh 😉
######## [ Proof / Exploit ] ################|=>
# Google Dork :
# allintext:"Powered by phpLiteAdmin | "
##################
# [!] Description:
------------------
phpLiteAdmin is suffer from multiple vulnerabilities / bugs in
v1.8.x to-> 1.9.x , the attacker can use some bug in the Script
to inject some remote SQL command/code , and Disclosure the Full Path.
Interesting to say 1.9.x when there are still 1.9.x versions to be released in the future. So you are sure we won’t fix your “bugs”? Probably you are right 😉
# Bugs :
#-------
# Authentication Bypass
# SQL Injection/Exec
# Full Path Disclosure
#######################
#### (1) Authentication Bypass :
--------------------------------
[!] php-code :
line 38->39 :::::::::::::::::
//password to gain access
$password = "admin";
:::::::::::::::::::::::::::::
- not affected on all targets, just change the password to fix it
[+] http://[target]/[path]/phpliteadmin.php[*] password : admin
I didn’t know we call it an “Authentication Bypass” if we use the authentication system by entering the correct password. Yeah, phpLiteAdmin has a default password, which is “admin”. No secret here. I mean, anybody keeping the default password on a publicly accessible installation should know that other people could get access. Current version of phpLiteAdmin even shows you a warning if you still use the default pw.
No “bug” or “vulnerability” at all.
#### (2) Full Path Disclosure :
-------------------------------
[+] http://[target]/[path]/phpliteadmin.php?view=import[!] & Import File with (NULL/Bad) Content =>
- you get some sql error msg with the full path of phpliteadmin.php
ex: '-------------
Warning: PDO::exec(): SQLSTATE[HY000]: General error:
trying to execute an empty query in C:\Program Files\EasyPHP-12.1\www\phpliteadmin.php on line 987
____________________________________
Warning: SQLiteDatabase::queryExec() [sqlitedatabase.queryexec]: Cannot execute empty query.
in /homepages/20/d421371141/htdocs/pauleschoen.com/cgi-bin/phpliteadmin.php on line 646
------------------'
LOL. That’s one of the most difficult ways to make phpLiteAdmin produce a PHP error message 😉
Probably you should configure your webserver correctly. Everybody who enables php-ini directive “display_errors” on a public server effectively provokes a “full path disclosure” somewhere. Maybe you should better publish an exploit for php itself 😉
Okay, seriously: We could use ini_set to make sure phpLiteAdmin won’t show any php errors. We probably will. But nevertheless, on about any php-server, you’ll find another script where you can provoke a php-error.
I am not saying it is good that these errors can happen at all. Of course it’d be better to improve checking of input and catch errors properly. This would be a real issue. But not a “vulnerability”. If these errors get displayed, your webserver is configured in a vulnerable way, which is not the fault of phpLiteAdmin.
#### (3) SQL Injection :
------------------------
php-code ::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::
$query = "SELECT * FROM ".$db->quote_id($_GET['table'])." WHERE ROWID = ".$pks[$j];
:::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::::
[+] http://[target]/[path]/phpliteadmin.php?action=row_view&table='[&] http://[target]/[path]/phpliteadmin.php?action=row_view&table=' [ SQLi ]
If you publish an SQL injection exploit, why don’t you insert some real SQL as a proof of concept? Maybe because what you “found” here in fact is no SQL injection at all?
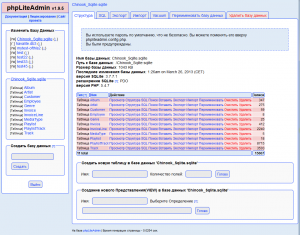
The function quote_id() will make sure you cannot inject some other SQL command. Of course you can “inject” some invalid table-name, which will make phpLiteAdmin show up some errors, as your “proof image” shows. So another complicated way of producing an error message. Congratulations! But you cannot inject a “DROP Table” here or something like that.
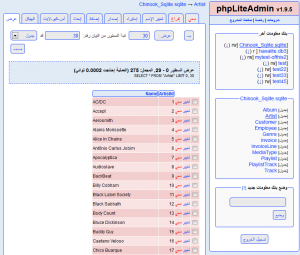
Moreover, it is ridiculous to even search for an SQL injection in phpLiteAdmin. If you are logged into phpLiteAdmin, you can of course perform any SQL command. That is what phpLiteAdmin is made for. It even gives you a GUI to perform SQL queries in a comfortable way. No need to inject them via parameters.
As long as you cannot inject an SQL query without authenticating properly, any “SQL injection” in phpLiteAdmin is not a security vulnerability but a normal issue. If some table has a special name, e.g. containing quotes, we need to make sure the name is escaped properly so phpLiteAdmin works as expected. But this is not the case here: quote_id() will make sure every table-name will be escaped properly. No issue here at all.
#### (4) Exec SQL code :
------------------------
Go to :
[*] http://[target]/[path]/phpliteadmin.php?view=sql-& put the SQL Code in the text-area (Run SQL query/queries :)
and click 'GO' to exec ;) .
LOL. That’s a really funny one. You might call this a vulnerability, I’d call it a feature.
Don’t you show yourself here that issue 3 is ridiculous?
So I am not sure if this exploit really was meant seriously or if it was meant as a joke. It made me laugh anyway.
I hope you enjoyed it as well. Keep on exploiting!